IoT/Connected Device visibility
Today’s enterprise networks are complex environments with different types of wired and wireless devices being connected and disconnected. Therefore, an effective device discovery system that enables us to identify device type, maker, model and OS/firmware is crucial for successful security management.
The current device discovery solutions have been mainly focused on identifying and monitoring servers, workstation PCs, laptops and infrastructure devices such as network firewalls, switches and routers. This is due to the fact that the most valuable information assets of organizations are being stored, processed and transferred over those devices, hence making them the prime target of security breaches and intrusions. However, a new trend has been emerging in the past 4 years, where attackers have been targeting purpose-built connected devices such as network printers and video conferencing systems as an entry point and data exfiltration node. IT asset discovery solutions cannot properly identify these IoT devices for the following reasons:
- Proprietary protocols are often used for managing and monitoring such devices that are not known to the asset discovery solution
- Agent based asset discovery is not possible because most of the connected devices are resource constrained systems with proprietary operating systems that do not allow installation of discovery agent software on them
- Device discovery is often limited to the devices with a history of known vulnerabilities
- The fuzz testing methods used by these solutions often time caused device operating system crash and reliability issues
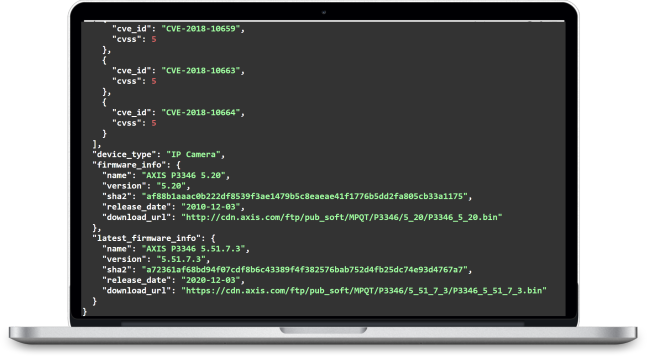
- Accurate identification of IoT device manufacturer, model name, device type, device end of life status, firmware version and firmware release date
- Safe and in-depth vulnerability assessment of identified device including publicly known vulnerabilities (CVE) and unknown vulnerabilities in device firmware code including vulnerable 3rd party components, default credentials, crypto keys, certificates and default configuration issues
IoTVAS vulnerability detection engine is specifically built for enterprise IoT/connected device security and is based on our global-scale proprietary firmware vulnerability knowledgebase that is constantly growing and evolving automatically as our analysis engine automatically collects and processes new device firmware binaries on behalf of device manufacturers and consumers. Through this knowledgebase, our vulnerability detection engine gains in-depth visibility into the applications running on a target IoT/connected device, their vulnerabilities and associated risks. IoTVAS also keeps tracking vulnerable devices as they change IP addresses or move around the network.